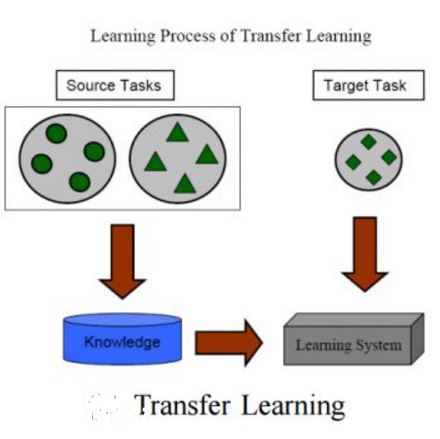
The vulnerability of smartphones to cyberattacks has been a severe concern to users arising from the integrity of installed applications (\textit{apps}). Although applications are to provide legitimate and diversified on-the-go services, harmful and dangerous ones have also uncovered the feasible way to penetrate smartphones for malicious behaviors. Thorough application analysis is key to revealing malicious intent and providing more insights into the application behavior for security risk assessments. Such in-depth analysis motivates employing deep neural networks (DNNs) for a set of features and patterns extracted from applications to facilitate detecting potentially dangerous applications independently. This paper presents an Analytic-based deep neural network, Android Malware detection (ADAM), that employs a fine-grained set of features to train feature-specific DNNs to have consensus on the application labels when their ground truth is unknown. In addition, ADAM leverages the transfer learning technique to obtain its adjustability to new applications across smartphones for recycling the pre-trained model(s) and making them more adaptable by model personalization and federated learning techniques. This adjustability is also assisted by federated learning guards, which protect ADAM against poisoning attacks through model analysis. ADAM relies on a diverse dataset containing more than 153000 applications with over 41000 extracted features for DNNs training. The ADAM's feature-specific DNNs, on average, achieved more than 98% accuracy, resulting in an outstanding performance against data manipulation attacks.
翻译:智能手机对网络攻击的脆弱性一直是用户因安装应用程序(\ textit{apps})的完整性而产生的严重关切。虽然应用程序的目的是提供合法和多样化的现成服务,但有害和危险的应用程序也揭示了为恶意行为穿透智能手机的可行途径。彻底应用分析是揭示恶意意图和对安全风险评估应用行为提供更深入了解的关键。这种深入分析鼓励利用深神经网络(DNNs)来利用从应用中提取的一套特性和模式来方便独立检测潜在危险的应用程序。本文展示了基于分析的深神经网络,Androd Maware探测(ADM),使用一套精细精细的功能来培训特定特性的DNNNS,以便在其地面真相不明时能够就应用程序标签达成共识。此外,ADAM利用转移学习技术来使其适应智能手机的新应用,使其通过模型个人化和美化学习技术更适应这些特性。这一可调整性模型还有助于防止基于特定特性的DNDAM系统(ADAM)进行不甚易变现的数据分析。