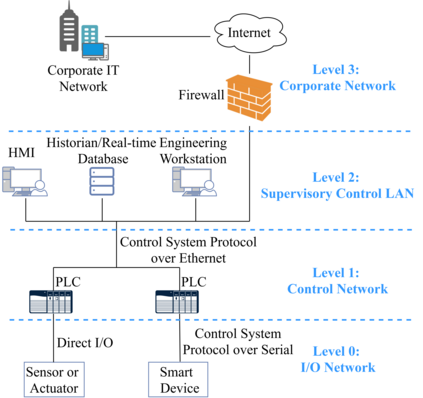
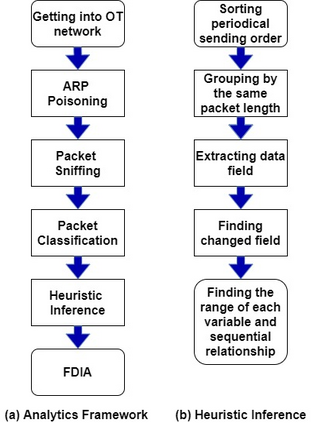
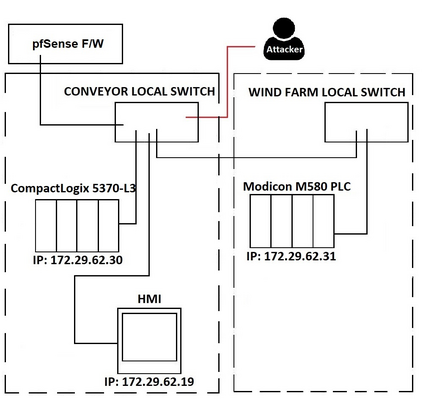
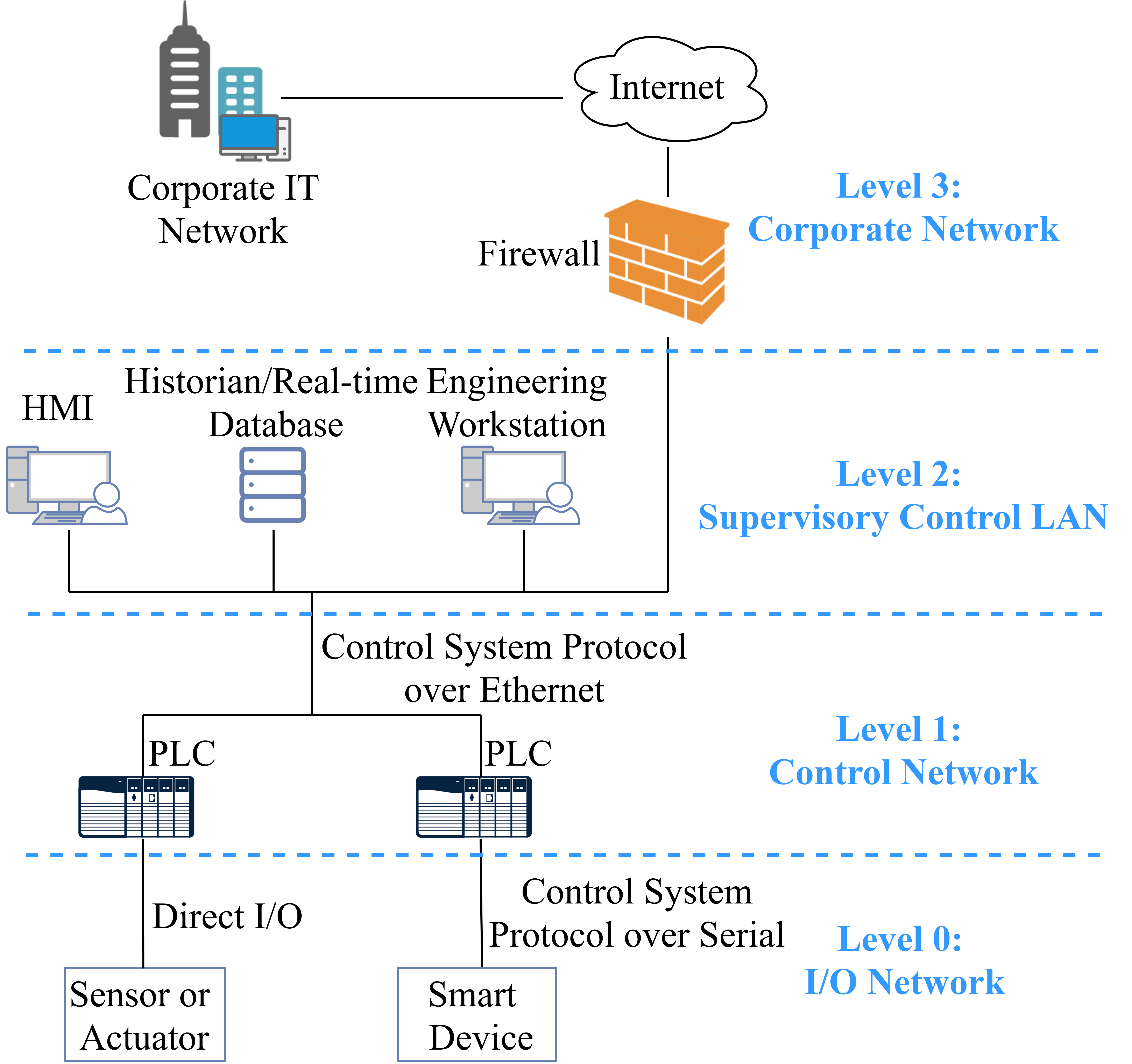
Industrial control systems (ICS) of critical infrastructure are increasingly connected to the Internet for remote site management at scale. However, cyber attacks against ICS - especially at the communication channels between humanmachine interface (HMIs) and programmable logic controllers (PLCs) - are increasing at a rate which outstrips the rate of mitigation. In this paper, we introduce a vendor-agnostic analytics framework which allows security researchers to analyse attacks against ICS systems, even if the researchers have zero control automation domain knowledge or are faced with a myriad of heterogenous ICS systems. Unlike existing works that require expertise in domain knowledge and specialised tool usage, our analytics framework does not require prior knowledge about ICS communication protocols, PLCs, and expertise of any network penetration testing tool. Using `digital twin' scenarios comprising industry-representative HMIs, PLCs and firewalls in our test lab, our framework's steps were demonstrated to successfully implement a stealthy deception attack based on false data injection attacks (FDIA). Furthermore, our framework also demonstrated the relative ease of attack dataset collection, and the ability to leverage well-known penetration testing tools. We also introduce the concept of `heuristic inference attacks', a new family of attack types on ICS which is agnostic to PLC and HMI brands/models commonly deployed in ICS. Our experiments were also validated on a separate ICS dataset collected from a cyber-physical scenario of water utilities. Finally, we utilized time complexity theory to estimate the difficulty for the attacker to conduct the proposed packet analyses, and recommended countermeasures based on our findings.
翻译:关键基础设施的工业控制系统(ICS)日益与互联网连接,以进行规模的远程站点管理;然而,对ICS的网络攻击,特别是在人体机器接口和可编程逻辑控制器之间的通信渠道,正在以高于减缓速度的速度增加,而这种攻击,特别是在人机接口和可编程逻辑控制器之间的通信渠道,正在以高于减缓速度的速度增加;在本文中,我们采用了一个供应商-不可知性分析框架,使安全研究人员能够分析对ICS系统的攻击,即使研究人员拥有零控制自动化域知识,或面临大量不均匀的ICS系统。 与目前需要领域知识和专门工具使用方面专门知识的工程不同,我们的分析框架并不要求事先了解ICS通信通信通信通信协议的通信程序、PLCs以及任何网络渗透测试工具的专业知识。 使用由具有工业代表性的HMI、PLCs和防火墙构成的“数字组合”假设,我们的框架还展示了成功实施基于虚假数据输入攻击的隐性欺骗性攻击(ICSA)估计。 此外,我们的框架还表明攻击数据收集和专门工具的相对容易进行数据采集,我们关于攻击的模型的模型的系统对攻击的系统进行最终测试工具进行。