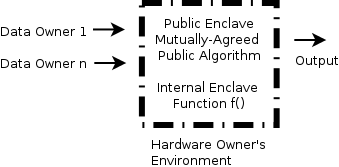
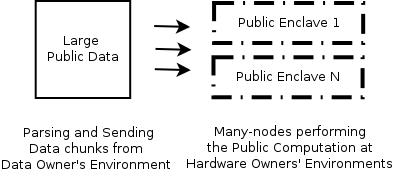
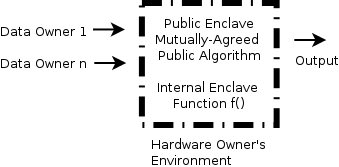
Digital services have been offered through remote systems for decades. The questions of how these systems can be built in a trustworthy manner and how their security properties can be understood are given fresh impetus by recent hardware developments, allowing a fuller, more general, exploration of the possibilities than has previously been seen in the literature. Drawing on and consolidating the disparate strains of research, technologies and methods employed throughout the adaptation of confidential computing, we present a novel, dedicated Confidential Remote Computing (CRC) model. CRC proposes a compact solution for next-generation applications to be built on strong hardware-based security primitives, control of secure software products' trusted computing base, and a way to make correct use of proofs and evidence reports generated by the attestation mechanisms. The CRC model illustrates the trade-offs between decentralisation, task size and transparency overhead. We conclude the paper with six lessons learned from our approach, and suggest two future research directions.
翻译:数十年来,通过远程系统提供了数字服务,最近硬件的发展为如何以可信赖的方式建立这些系统以及如何理解其安全特性提供了新的动力,使得能够更全面、更普遍地探索文献中以往所见的各种可能性。利用和巩固在调整保密计算过程中使用的各种不同的研究、技术和方法,我们提出了一个新的、专门的保密远程计算(CRC)模型。儿童权利委员会建议为下一代应用提出一个紧凑的解决办法,这些应用将建立在强大的硬件基础安全原始之上,控制安全软件产品所信任的计算基础,以及正确使用证明机制产生的证据和证据报告的方法。《儿童权利公约》模型说明了分散、任务规模和透明度间接费用之间的权衡。我们用从我们的方法中吸取的六种经验来结束该文件,并提出两个未来研究方向。