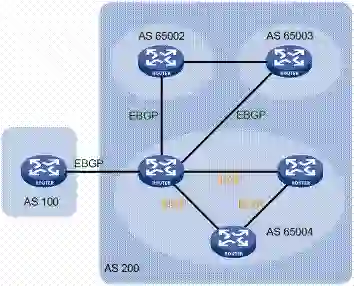
The Internet is a critical resource in the day-to-day life of billions of users. To support the growing number of users and their increasing demands, operators have to continuously scale their network footprint -- e.g., by joining Internet Exchange Points -- and adopt relevant technologies -- such as IPv6. IPv6, however, has a vastly larger address space compared to its predecessor, which allows for new kinds of attacks on the Internet routing infrastructure. In this paper, we present Kirin: a BGP attack that sources millions of IPv6 routes and distributes them via thousands of sessions across various IXPs to overflow the memory of border routers within thousands of remote ASes. Kirin's highly distributed nature allows it to bypass traditional route-flooding defense mechanisms, such as per-session prefix limits or route flap damping. We analyze the theoretical feasibility of the attack by formulating it as a Integer Linear Programming problem, test for practical hurdles by deploying the infrastructure required to perform a small-scale Kirin attack using 4 IXPs, and validate our assumptions via BGP data analysis, real-world measurements, and router testbed experiments. Despite its low deployment cost, we find Kirin capable of injecting lethal amounts of IPv6 routes in the routers of thousands of ASes.
翻译:互联网是数十亿用户日常生活中的关键资源。为了支持越来越多的用户及其不断增加的需求,运营商必须不断扩大网络足迹,例如加入互联网交换点,并采用相关技术,例如IPv6.6 IPv6, 然而,与其前身相比,互联网的地址空间要大得多,允许对互联网路由基础设施进行新型袭击。在本文中,我们介绍基林:BGP袭击,其中数百万个IPv6线路的源头,通过各种九连五相之间的数千次会议将其分发,以将边境路由器的记忆溢满数千个远程ASes。基林高度分布性允许它绕过传统的路况阻隔防御机制,例如每条路边的预设限制或断路段。我们分析这次袭击的理论可行性,将它写成Integer线性规划问题,通过利用4IXPs部署必要的基础设施进行小规模Kirin袭击来测试实际障碍,并通过BGP数据分析、真实世界测量和路径测试系统测试数千个致命路径的路径。尽管其成本低,但我们通过BGP数据分析、真实世界测测算6 能够部署的IP6 。