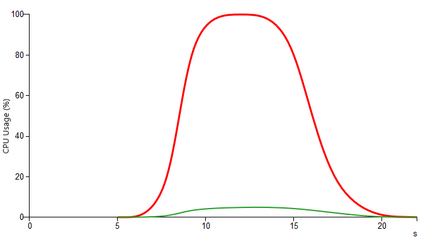
Online malware scanners are one of the best weapons in the arsenal of cybersecurity companies and researchers. A fundamental part of such systems is the sandbox that provides an instrumented and isolated environment (virtualized or emulated) for any user to upload and run unknown artifacts and identify potentially malicious behaviors. The provided API and the wealth of information inthe reports produced by these services have also helped attackers test the efficacy of numerous techniques to make malware hard to detect.The most common technique used by malware for evading the analysis system is to monitor the execution environment, detect the presence of any debugging artifacts, and hide its malicious behavior if needed. This is usually achieved by looking for signals suggesting that the execution environment does not belong to a the native machine, such as specific memory patterns or behavioral traits of certain CPU instructions. In this paper, we show how an attacker can evade detection on such online services by incorporating a Proof-of-Work (PoW) algorithm into a malware sample. Specifically, we leverage the asymptotic behavior of the computational cost of PoW algorithms when they run on some classes of hardware platforms to effectively detect a non bare-metal environment of the malware sandbox analyzer. To prove the validity of this intuition, we design and implement the POW-HOW framework, a tool to automatically implement sandbox detection strategies and embed a test evasion program into an arbitrary malware sample. Our empirical evaluation shows that the proposed evasion technique is durable, hard to fingerprint, and reduces existing malware detection rate by a factor of 10. Moreover, we show how bare-metal environments cannot scale with actual malware submissions rates for consumer services.
翻译:在线恶意软件扫描器是网络安全公司和研究人员武库中最好的武器之一。 这种系统的一个基本部分是沙箱,它为任何用户上传和运行未知文物以及识别潜在恶意行为提供了一个工具化和孤立的环境(虚拟化或模仿),使任何用户能够上传和运行未知文物,并识别潜在的恶意行为。所提供的API和这些服务所产生报告中的大量信息也帮助攻击者测试了使恶意软件难以检测的多种技术的功效。 恶意软件逃避分析系统最常用的方法是监测执行环境,发现任何调试的文物的存在,并在需要时隐藏其恶意行为。 通常通过寻找信号,表明执行环境不属于本地机器,例如具体的记忆模式或某些CPU指令的行为特性。 在本文中,我们展示攻击者如何通过将“证据-工作”算法(POW)算法纳入一个错误抽样。 具体来说,我们无法利用POW算法的计算成本的直观行为,当它们运行在某类内部成本检测中时,我们无法降低实际成本值的计算成本。