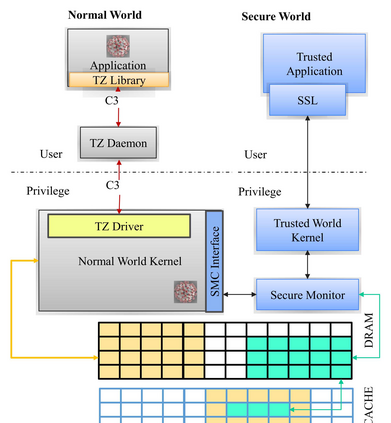
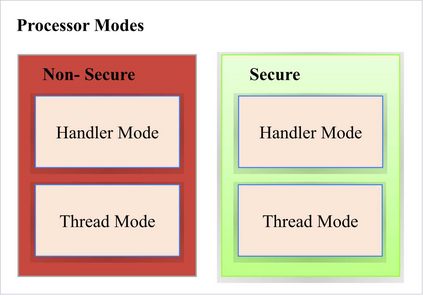
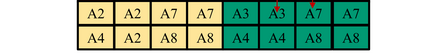
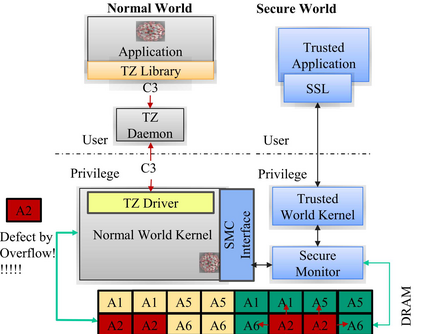
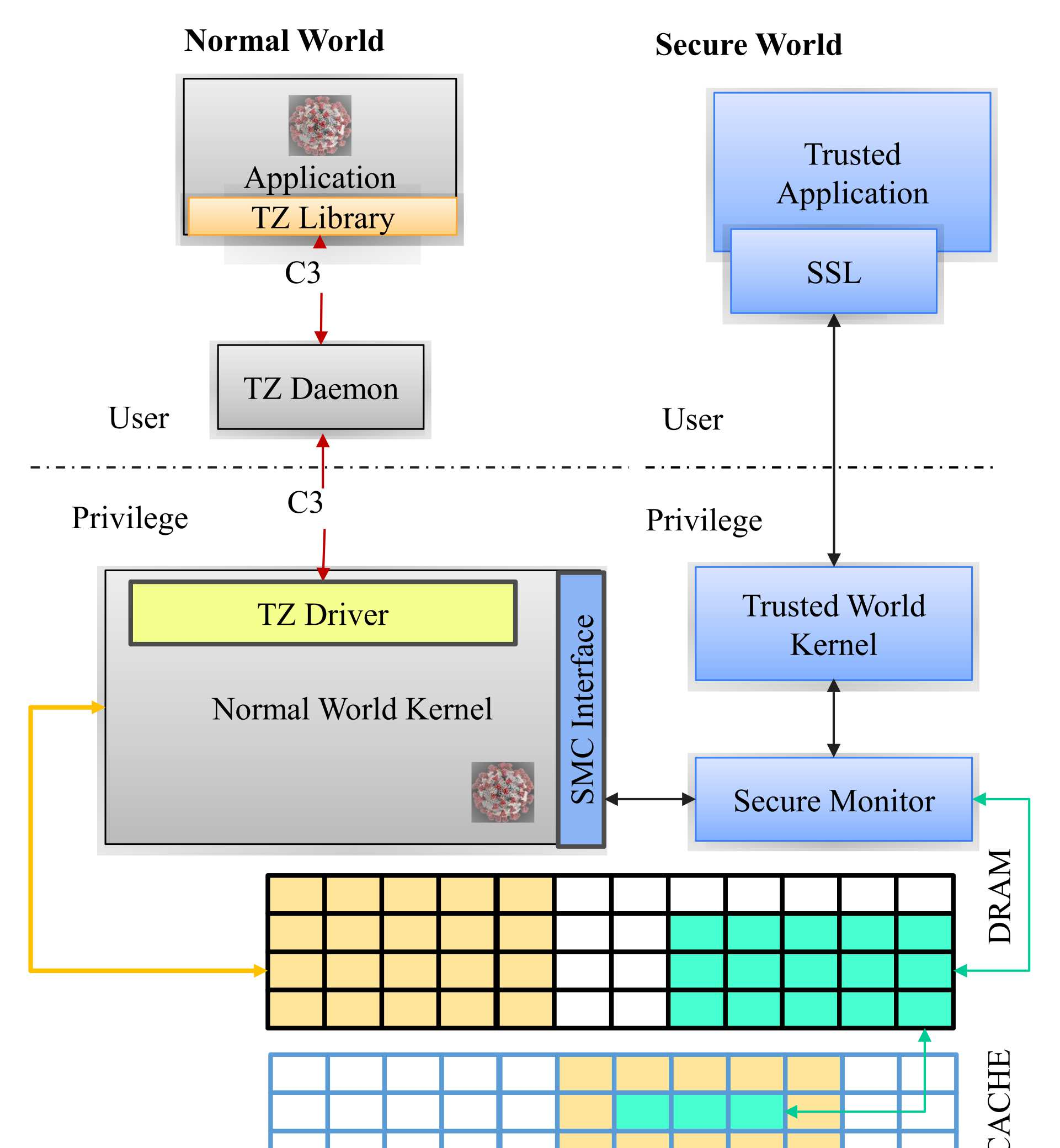
With the significant development of the Internet of Things and low-cost cloud services, the sensory and data processing requirements of IoT systems are continually going up. TrustZone is a hardware-protected Trusted Execution Environment (TEE) for ARM processors specifically designed for IoT handheld systems. It provides memory isolation techniques to protect trusted application data from being exploited by malicious entities. In this work, we focus on identifying different vulnerabilities of the TrustZone extension of ARM Cortex-M processors. Then design and implement a threat model to execute those attacks. We have found that TrustZone is vulnerable to buffer overflow-based attacks. We have used this to create an attack called MOFlow and successfully leaked the data of another trusted app. This is done by intentionally overflowing the memory of one app to access the encrypted memory of other apps inside the secure world. We have also found that, by not validating the input parameters in the entry function, TrustZone has exposed a security weakness. We call this Achilles heel and present an attack model showing how to exploit this weakness too. Our proposed novel attacks are implemented and successfully tested on two recent ARM Cortex-M processors available on the market (M23 and M33).
翻译:随着物的互联网和低成本云服务的重大发展,IoT系统的感官和数据处理要求正在不断上升。信任区是为IoT手持系统专门设计的ARM处理器而设计的硬件保护信任执行环境(TEE),它提供了记忆隔离技术,以保护可信赖的应用数据不被恶意实体利用。在这项工作中,我们侧重于查明信任区的ARM Cortex-M处理器扩展部分的不同弱点。然后设计和实施一个威胁模式来实施这些攻击。我们发现信任区易受缓冲溢出的攻击。我们利用这个区域制造了一个名为MOFlow的袭击,成功地泄漏了另一个可信赖的应用程序的数据。这是通过故意将一个应用程序的记忆溢出,以获取安全世界内其他应用程序的加密记忆。我们还发现,由于无法验证输入功能中的输入参数, TrustZone暴露了安全弱点。我们称之为Achilles heel, 并展示了一个攻击模型,说明如何利用这一弱点。我们拟议的新式攻击M23和Mex33号最近被安装并成功测试了。