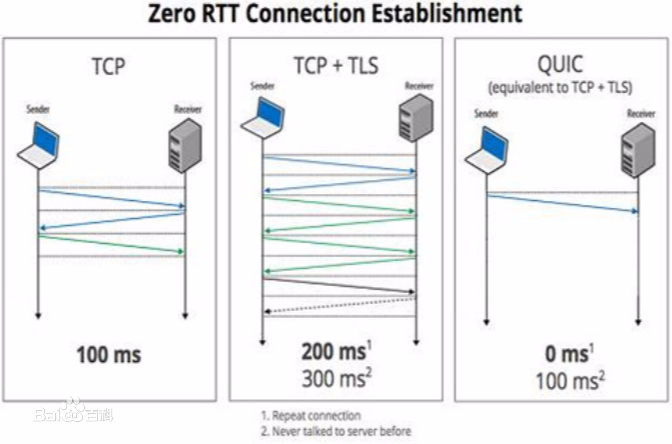
Cryptographic protocols have been widely used to protect the user's privacy and avoid exposing private information. QUIC (Quick UDP Internet Connections), including the version originally designed by Google (GQUIC) and the version standardized by IETF (IQUIC), as alternatives to the traditional HTTP, demonstrate their unique transmission characteristics: based on UDP for encrypted resource transmitting, accelerating web page rendering. However, existing encrypted transmission schemes based on TCP are vulnerable to website fingerprinting (WFP) attacks, allowing adversaries to infer the users' visited websites by eavesdropping on the transmission channel. Whether GQUIC and IQUIC can effectively resist such attacks is worth investigating. In this paper, we study the vulnerabilities of GQUIC, IQUIC, and HTTPS to WFP attacks from the perspective of traffic analysis. Extensive experiments show that, in the early traffic scenario, GQUIC is the most vulnerable to WFP attacks among GQUIC, IQUIC, and HTTPS, while IQUIC is more vulnerable than HTTPS, but the vulnerability of the three protocols is similar in the normal full traffic scenario. Features transferring analysis shows that most features are transferable between protocols when on normal full traffic scenario. However, combining with the qualitative analysis of latent feature representation, we find that the transferring is inefficient when on early traffic, as GQUIC, IQUIC, and HTTPS show the significantly different magnitude of variation in the traffic distribution on early traffic. By upgrading the one-time WFP attacks to multiple WFP Top-a attacks, we find that the attack accuracy on GQUIC and IQUIC reach 95.4% and 95.5%, respectively, with only 40 packets and just using simple features, whereas reach only 60.7% when on HTTPS. We also demonstrate that the vulnerability of IQUIC is only slightly dependent on the network environment.
翻译:QUIC (Quick UDP Internet Connects), 包括谷歌(GQUIC)最初设计的版本和IETFT(IQUIC)标准化的版本,作为传统 HTTP 的替代方案,显示了它们独特的传输特点:基于UDP的加密资源传输,加快网页制作。然而,基于TCP的现有加密传输计划很容易受到网站指纹(WFP)攻击的伤害,允许对手通过在传输频道偷听来推断访问的用户网站的变异性。 GQUIC 和 IQIUIC 是否能够有效抵制这种攻击值得调查。 在本文件中,我们从交通分析的角度研究GQUIC、IQUIC 和HTPS 袭击的弱点:基于UDP的加密资源传输,加快网页创建。在早期交通情况中,GQUIC 的弱点和HTPS, IPFC 的变异性交通变异性分析显示,在正常交通变异性协议中, IMUIBI 的特性分析显示,在正常交通变异性规则中也显示ITC 。