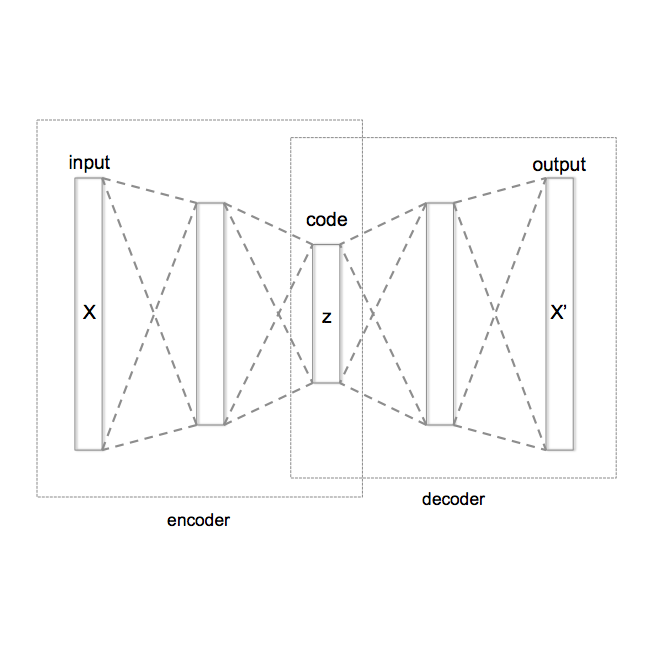
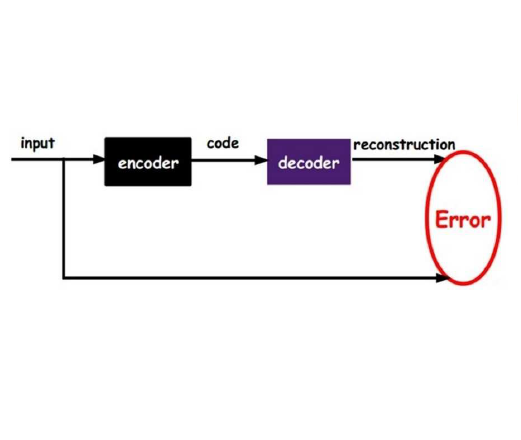
Although the use of pay-per-click mechanisms stimulates the prosperity of the mobile advertisement network, fraudulent ad clicks result in huge financial losses for advertisers. Extensive studies identify click fraud according to click/traffic patterns based on dynamic analysis. However, in this study, we identify a novel click fraud, named humanoid attack, which can circumvent existing detection schemes by generating fraudulent clicks with similar patterns to normal clicks. We implement the first tool ClickScanner to detect humanoid attacks on Android apps based on static analysis and variational AutoEncoder (VAE) with limited knowledge of fraudulent examples. We define novel features to characterize the patterns of humanoid attacks in the apps' bytecode level. ClickScanner builds a data dependency graph (DDG) based on static analysis to extract these key features and form a feature vector. We then propose a classification model only trained on benign datasets to overcome the limited knowledge of humanoid attacks. We leverage ClickScanner to conduct the first large-scale measurement on app markets (i.e.,120,000 apps from Google Play and Huawei AppGallery) and reveal several unprecedented phenomena. First, even for the top-rated 20,000 apps, ClickScanner still identifies 157 apps as fraudulent, which shows the prevalence of humanoid attacks. Second, it is observed that the ad SDK-based attack (i.e., the fraudulent codes are in the third-party ad SDKs) is now a dominant attack approach. Third, the manner of attack is notably different across apps of various categories and popularities. Finally, we notice there are several existing variants of the humanoid attack. Additionally, our measurements demonstrate the proposed ClickScanner is accurate and time-efficient (i.e., the detection overhead is only 15.35% of those of existing schemes).
翻译:虽然使用按每点击付费的机制可以刺激移动广告网络的繁荣,但欺诈性广告点击会给广告商带来巨大的财务损失。广泛的研究根据动态分析的动态分析,根据点击/交易模式,确定点击欺诈。然而,在本研究中,我们发现一个新点击欺诈,称为人体攻击,通过生成类似模式的欺诈性点击,可以绕过现有的检测计划。我们实施了第一个工具点击扫描器,以根据静态分析和变异性AutoEncoder(VAE)发现对Adroid Apps的人体攻击,但缺乏欺诈性实例。我们定义了在应用程序节码水平上描述人类攻击模式的新特点。ClickScanner根据静态分析,制作了一个数据依赖性图(DDGG),以提取这些关键特征并形成一个特性矢量矢量的特性矢量。我们提出一个只接受良性数据集的分类模型,以克服对人体攻击的有限知识。我们利用ClickScanner进行首次大规模调查(我们来自Goof Prial Prime攻击的120, ad Appealalalal atal acreal astection strational strational stration) stract sal strations) strevations is supal supal sal sal sal sal sal sal sal sal supaltime supald.